ABA Position Paper on Promoting Cyber Security
Promoting Cyber Security
ABSTRACT
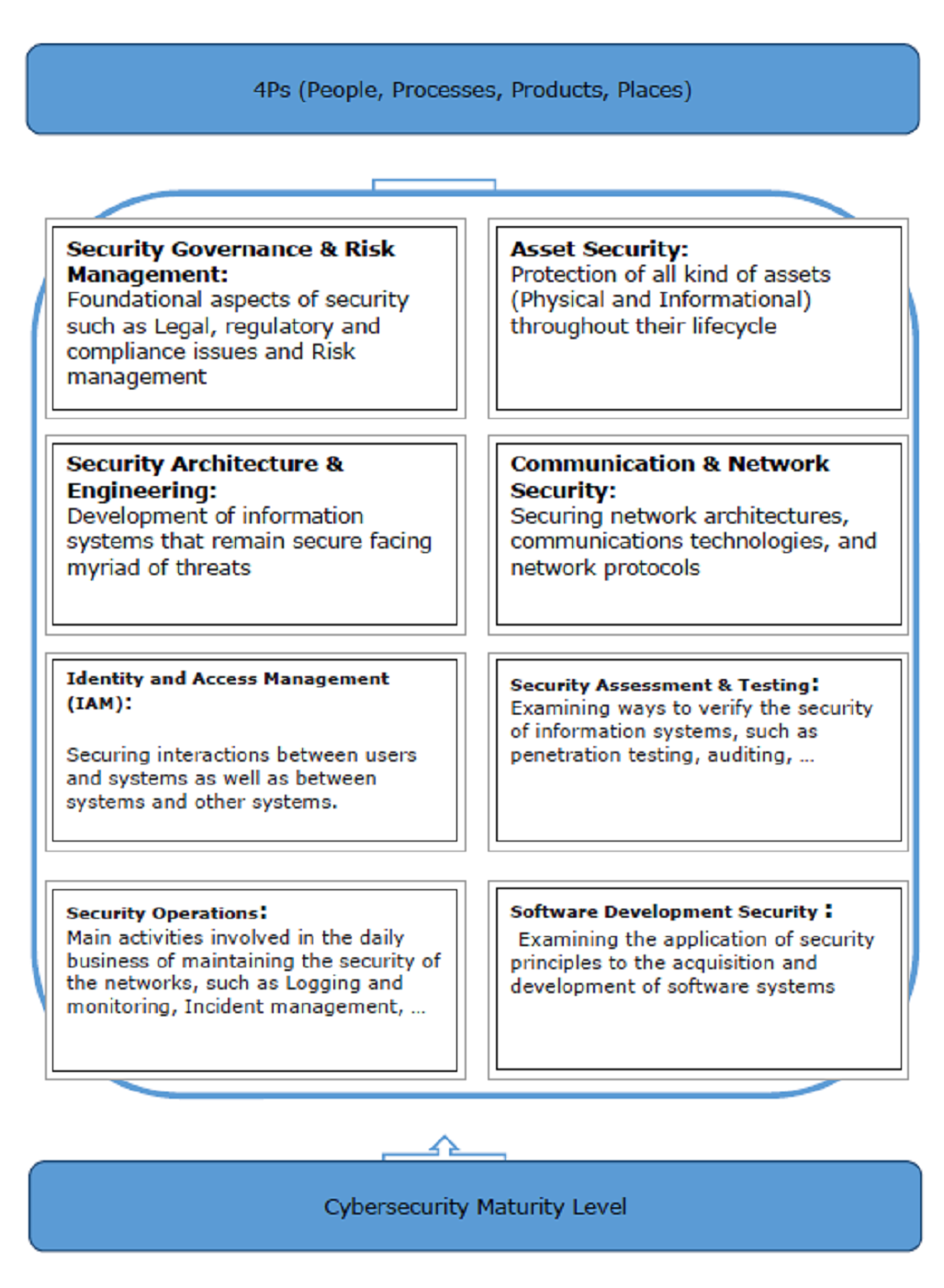
Figure 1: The BPI (Bank Pasargad Iran) security Frame Work
Some of the major tools and solutions used under the Cyber Security framework have been discussed in detail in this document.
(1) Bank Pasargad
(2) Dotin
(3) Content Delivery Network (CDN)
In line with the stringent security polices of the Bank, a private cloud and dedicated CDN seemed as the best option to maximize the cyber security of the bank. Usually, most companies that provide CDN services use their own public infrastructure in order to offer services to the banks.
In the case of Bank Pasargad, Dotin has provided the complete CDN solution on premises of Bank Pasargad. Dotin’s task was daunting since this was the first time a CDN was being implemented in Iran. The project was different from any CDN project that we know of around the world since in case of Bank Pasargad, Dotin had to deliver a dedicated infrastructure fully functional and operational under the supervision and management of the bank. After the implementation and golive, the vendor (Dotin) was to have no access to any bank information anymore.
There were two main goals of Bank Pasargad for implanting CDN. The first goal was increasing the performance and the quality of the web based services in the banks. Dotin offered a range of edge servers to Bank Pasargad as part of the CDN. The users are connected to the closest server to their geographical location and as a result, they experience a faster and higher quality of usage. The service reduced the average load time of Bank Pasargad’s online services by 40 to 70%. A page that would load in 1 second before implementing CDN now loads between 0.6 to 0.3 seconds.
The second goal was increasing the security of these services and the management of security of services in an integrated form. Since the implementation many attacks, including a DDos attack with the volume of 200 Gb/ps have been fended off. Furthermore, thousands of cyber-attacks to banking web services were fend off, using WAF (Web Application firewall). Several cyber attacks were blocked and among them the most recent ones were DDoS attack that were blocked.
(4) Cyber threat hunting
Our expoert analysts know how to coax their toolsets into finding the most dangerous threats. They have required ample knowledge of different types of malware, exploits and network protocols to navigate the large volume of data consisting of logs, metadata and packet capture (PCAP) data.
(5) Endpoint detection and response (EDR)
- Monitor and collect activity data from endpoints that could indicate a threat
- Analyze this data to identify threat patterns
- Automatically respond to identified threats to remove or contain them, and notify security personnel
- Forensics and analysis tools to research identified threats and search for suspicious activities
(6) Privileged Access Management (PAM)
(7) Security Operation Center (SOC)
For each of these events, the SOC decides how they will be managed and acted upon.
(8) Penetration Testing
(9) Enterprise Mobility + Security (EMS)
(10) Governance, Risk, Compliance (GRC)
(11) Red Team Excercise
(12) Conclusion
Prepared for the Asian Bankers Association by:

Mahdieh Noroozian
Chief Planning & Development Officer
Dotin
(in-house banking solution of Bank Pasargad)


